- Ssh Configuration File
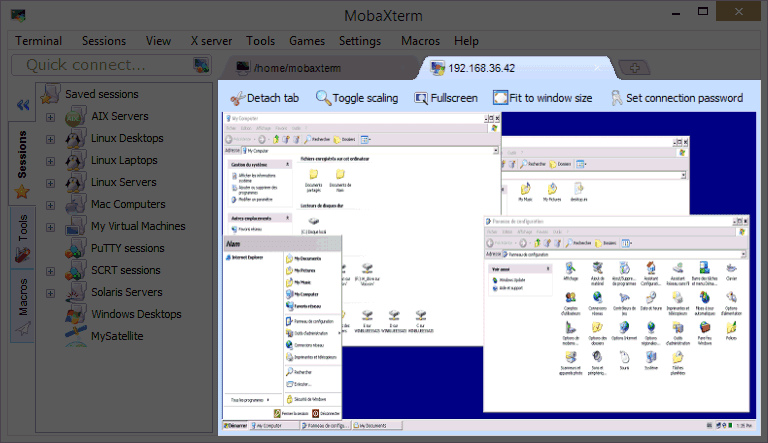
- Windows Global Ssh Config
- Jenkins Ssh Global Configuration
- Git Global Ssh Config
EnableSSHKeysign Setting this option to yes in the global client configuration file /etc/ssh/sshconfig enables the use of the helper program ssh-keysign (8) during HostbasedAuthentication. The argument must be yes or no (the default). This option should be placed in the non- hostspecific section. See ssh-keysign (8) for more information. My memo regarding Solaris/AIX/CentOS/Fedora/Debian/Ubuntu or something like those Unix-based OSs. GlobalKnownHostsFile Specifies one or more files to use for the global host key database, separated by whitespace. Ssh/config should be used if. Configuring the default ssh shell is done in the Windows registry by adding the full path to the shell executable to ComputerHKEYLOCALMACHINESOFTWAREOpenSSH in the string value DefaultShell. As an example, the following Powershell command. Global SSH, Purwokerto, Jawa Tengah, Indonesia. 8,720 likes 21 talking about this. The Best Provider of Premium Tunneling Accounts SSH, VPN, Shadowsocks, Proxy which absolutely FREE.
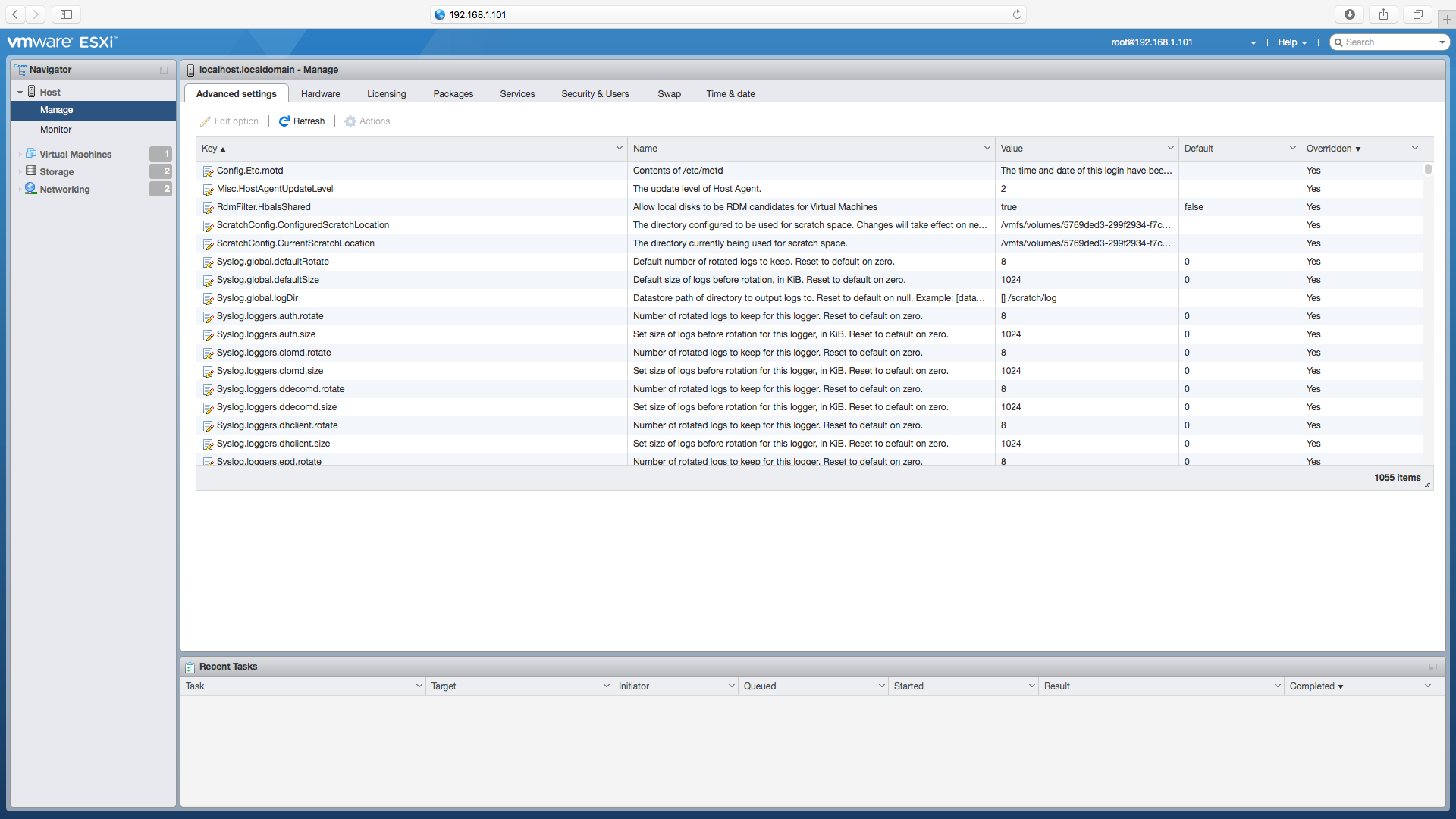
-->This topic covers the Windows-specific configuration for OpenSSH Server (sshd).
OpenSSH maintains detailed documentation for configuration options online at OpenSSH.com, which is not duplicated in this documentation set.
Configuring the default shell for OpenSSH in Windows
The default command shell provides the experience a user sees when connecting to the server using SSH.The initial default Windows is the Windows Command shell (cmd.exe).Windows also includes PowerShell and Bash, and third party command shells are also available for Windows and may be configured as the default shell for a server.
To set the default command shell, first confirm that the OpenSSH installation folder is on the system path.For Windows, the default installation folder is SystemDrive:WindowsDirectorySystem32openssh.The following commands shows the current path setting, and add the default OpenSSH installation folder to it.
| Command shell | Command to use |
|---|---|
| Command | path |
| PowerShell | $env:path |
Configuring the default ssh shell is done in the Windows registry by adding the full path to the shell executable to ComputerHKEY_LOCAL_MACHINESOFTWAREOpenSSH in the string value DefaultShell.
As an example, the following Powershell command sets the default shell to be PowerShell.exe:
Windows Configurations in sshd_config
In Windows, sshd reads configuration data from %programdata%sshsshd_config by default, or a different configuration file may be specified by launching sshd.exe with the -f parameter.If the file is absent, sshd generates one with the default configuration when the service is started.
The elements listed below provide Windows-specific configuration possible through entries in sshd_config.There are other configuration settings possible in that are not listed here, as they are covered in detail in the online Win32 OpenSSH documentation.
AllowGroups, AllowUsers, DenyGroups, DenyUsers
Controlling which users and groups can connect to the server is done using the AllowGroups, AllowUsers, DenyGroups and DenyUsers directives.The allow/deny directives are processed in the following order: DenyUsers, AllowUsers, DenyGroups, and finally AllowGroups.All account names must be specified in lower case.See PATTERNS in ssh_config for more information on patterns for wildcards.
When configuring user/group based rules with a domain user or group, use the following format: user?domain*.Windows allows multiple of formats for specifying domain principals, but many conflict with standard Linux patterns.For that reason, * is added to cover FQDNs.Also, this approach uses '?', instead of @, to avoid conflicts with the username@host format.
Work group users/groups and internet-connected accounts are always resolved to their local account name (no domain part, similar to standard Unix names).Domain users and groups are strictly resolved to NameSamCompatible format - domain_short_nameuser_name.All user/group based configuration rules need to adhere to this format.
Examples for domain users and groups
Examples for local users and groups
AuthenticationMethods
For Windows OpenSSH, the only available authentication methods are 'password' and 'publickey'.
AuthorizedKeysFile
The default is '.ssh/authorized_keys .ssh/authorized_keys2'. If the path is not absolute, it is taken relative to user's home directory (or profile image path). Ex. c:usersuser. Note that if the user belongs to the administrator group, %programdata%/ssh/administrators_authorized_keys is used instead.
ChrootDirectory (Support added in v7.7.0.0)
This directive is only supported with sftp sessions. A remote session into cmd.exe wouldn't honor this. To setup a sftp-only chroot server, set ForceCommand to internal-sftp. You may also set up scp with chroot, by implementing a custom shell that would only allow scp and sftp.
HostKey
The defaults are %programdata%/ssh/ssh_host_ecdsa_key, %programdata%/ssh/ssh_host_ed25519_key, %programdata%/ssh/ssh_host_dsa_key, and %programdata%/ssh/ssh_host_rsa_key. If the defaults are not present, sshd automatically generates these on a service start.
Match
Note that pattern rules in this section. User and group names should be in lower case.
PermitRootLogin
Not applicable in Windows. To prevent administrator login, use Administrators with DenyGroups directive.
SyslogFacility
If you need file based logging, use LOCAL0. Logs are generated under %programdata%sshlogs.For any other value, including the default value, AUTH directs logging to ETW. For more info, see Logging Facilities in Windows.
Not supported
The following configuration options are not available in the OpenSSH version that ships in Windows Server 2019 and Windows 10 1809:
- AcceptEnv
- AllowStreamLocalForwarding
- AuthorizedKeysCommand
- AuthorizedKeysCommandUser
- AuthorizedPrincipalsCommand
- AuthorizedPrincipalsCommandUser
- Compression
- ExposeAuthInfo
- GSSAPIAuthentication
- GSSAPICleanupCredentials
- GSSAPIStrictAcceptorCheck
- HostbasedAcceptedKeyTypes
- HostbasedAuthentication
- HostbasedUsesNameFromPacketOnly
- IgnoreRhosts
- IgnoreUserKnownHosts
- KbdInteractiveAuthentication
- KerberosAuthentication
- KerberosGetAFSToken
- KerberosOrLocalPasswd
- KerberosTicketCleanup
- PermitTunnel
- PermitUserEnvironment
- PermitUserRC
- PidFile
- PrintLastLog
- RDomain
- StreamLocalBindMask
- StreamLocalBindUnlink
- StrictModes
- X11DisplayOffset
- X11Forwarding
- X11UseLocalhost
- XAuthLocation
Azure DevOps Services | Azure DevOps Server 2020 | Azure DevOps Server 2019 | TFS 2018 - TFS 2015
Connect to your Git repos through SSH on macOS, Linux, or Windows to securely connect using HTTPS authentication. On Windows, we recommended the use of Git Credential Manager Core or Personal Access Tokens.
Important
SSH URLs have changed, but old SSH URLs will continue to work. If you have already set up SSH, you should update your remote URLs to the new format:
- Verify which remotes are using SSH by running
git remote -vin your Git client. - Visit your repository on the web and select the Clone button in the upper right.
- Select SSH and copy the new SSH URL.
- In your Git client, run:
git remote set-url <remote name, e.g. origin> <new SSH URL>. Alternatively, in Visual Studio, go to Repository Settings, and edit your remotes.
Note

As of Visual Studio 2017, SSH can be used to connect to Azure DevOps Git repos.

How SSH key authentication works
SSH public key authentication works with an asymmetric pair of generated encryption keys. The public key is shared with Azure DevOps and used to verify the initial ssh connection. The private key is kept safe and secure on your system.
Set up SSH key authentication
The following steps cover configuration of SSH key authentication on the following platforms:
- Linux
- macOS running at least Leopard (10.5)
- Windows systems running Git for Windows
Configure SSH using the command line. bash is the common shell on Linux and macOS and the Git for Windows installation adds a shortcut to Git Bash in the Start menu.Other shell environments will work, but are not covered in this article.
Step 1: Create your SSH keys
Note
If you have already created SSH keys on your system, skip this step and go to configuring SSH keys.
The commands here will let you create new default SSH keys, overwriting existing default keys. Before continuing, check your~/.ssh folder (for example, /home/jamal/.ssh or C:Usersjamal.ssh) and look for the following files:
- id_rsa
- id_rsa.pub
Ssh Configuration File
If these files exist, then you have already created SSH keys. You can overwrite the keys with the following commands, or skip this step and go to configuring SSH keys to reuse these keys.
Create your SSH keys with the ssh-keygen command from the bash prompt. This command will create a 2048-bit RSA key for use with SSH. You can give a passphrasefor your private key when prompted—this passphrase provides another layer of security for your private key.If you give a passphrase, be sure to configure the SSH agent to cache your passphrase so you don't have to enter it every time you connect.
This command produces the two keys needed for SSH authentication: your private key ( id_rsa ) and the public key ( id_rsa.pub ). It is important to never share the contents of your private key. If the private key iscompromised, attackers can use it to trick servers into thinking the connection is coming from you.
Step 2: Add the public key to Azure DevOps Services/TFS
Associate the public key generated in the previous step with your user ID.
Open your security settings by browsing to the web portal and selecting your avatar in the upper right of theuser interface. Select SSH public keys in the menu that appears.
Select + New Key.
Copy the contents of the public key (for example, id_rsa.pub) that you generated into the Public Key Data field.
Important
Avoid adding whitespace or new lines into the Key Data field, as they can cause Azure DevOps Services to use an invalid public key. When pasting in the key, a newline often is added at the end. Be sure to remove this newline if it occurs.
Give the key a useful description (this description will be displayed on the SSH public keys page for your profile) so that you can remember it later. Select Save to store the public key.Once saved, you cannot change the key. You can delete the key or create a new entry for another key. There are no restrictions on how many keys you can add to your user profile. Also note that SSH keys stored in Azure DevOps expire after five years. If your key expires, you may upload a new key or the same one to continue accessing Azure DevOps via SSH.
Test the connection by running the following command:
ssh -T git@ssh.dev.azure.com.If everything is working correctly, you'll receive a response which says:remote: Shell access is not supported.If not, see the section on Questions and troubleshooting.
Step 2: Add the public key to Azure DevOps
Associate the public key generated in the previous step with your user ID.
Open your security settings by browsing to the web portal and selecting your avatar in the upper right of theuser interface. Select Security in the menu that appears.
Select + New Key.
Copy the contents of the public key (for example, id_rsa.pub) that you generated into the Public Key Data field.
Important
Avoid adding whitespace or new lines into the Key Data field, as they can cause Azure DevOps Services to use an invalid public key. When pasting in the key, a newline often is added at the end. Be sure to remove this newline if it occurs.
Give the key a useful description (this description will be displayed on the SSH public keys page for your profile) so that you can remember it later. Select Save to store the public key. Once saved, you cannot change the key. You can delete the key or create a new entry for another key. There are no restrictions on how many keys you can add to your user profile.
Test the connection by running the following command:
ssh -T git@ssh.dev.azure.com.If everything is working correctly, you'll receive a response which says:remote: Shell access is not supported.If not, see the section on Questions and troubleshooting.
Step 3: Clone the Git repository with SSH
Note
To connect with SSH from an existing cloned repo, see updating your remotes to SSH.
Copy the SSH clone URL from the web portal. In this example, the SSL clone URL is for a repo in an organization named fabrikam-fiber, as indicated by the first part of the URL after
dev.azure.com.Note
Project URLs have changed with the release of Azure DevOps Services and now have the format
dev.azure.com/{your organization}/{your project}, but you can still use the existingvisualstudio.comformat. For more information, see Visual Studio Team Services is now Azure DevOps Services.Run
git clonefrom the command prompt.
SSH may display the server's SSH fingerprint and ask you to verify it.You should verify that the displayed fingerprint matches one of the fingerprints in the SSH public keys page.
SSH displays this fingerprint when it connects to an unknown host to protect you from man-in-the-middle attacks.Once you accept the host's fingerprint, SSH will not prompt you again unless the fingerprint changes.
When you are asked if you want to continue connecting, type yes. Git will clone the repo and set up the origin remote to connect with SSH for future Git commands.
Tip
To prevent problems, Windows users should run a command to have Git reuse their SSH key passphrase.
Questions and troubleshooting
Q: After running git clone, I get the following error. What should I do?
A: Manually record the SSH key by running:ssh-keyscan -t rsa domain.com >> ~/.ssh/known_hosts
Q: How can I have Git remember the passphrase for my key on Windows?
A: Run the following command included in Git for Windows to start up the ssh-agent process in PowerShell or the Windows Command Prompt. ssh-agent will cacheyour passphrase so you don't have to provide it every time you connect to your repo.
If you're using the Bash shell (including Git Bash), start ssh-agent with:
Q: I use PuTTY as my SSH client and generated my keys with PuTTYgen. Can I use these keys with Azure DevOps Services?
A: Yes. Load the private key with PuTTYgen, go to Conversions menu and select Export OpenSSH key.Save the private key file and then follow the steps to set up non-default keys.Copy your public key directly from the PuTTYgen window and paste into the Key Data field in your security settings.
Q: How can I verify that the public key I uploaded is the same key as I have locally?
A: You can verify the fingerprint of the public key uploaded with the one displayed in your profile through the following ssh-keygen command run against your public key usingthe bash command line. You will need to change the path and the public key filename if you are not using the defaults.
You can then compare the MD5 signature to the one in your profile. This check is useful if you have connection problems or have concerns about incorrectlypasting in the public key into the Key Data field when adding the key to Azure DevOps Services.
Q: How can I start using SSH in a repository where I am currently using HTTPS?
A: You'll need to update the origin remote in Git to change over from a HTTPS to SSH URL. Once you have the SSH clone URL, run the following command:
You can now run any Git command that connects to origin.
Q: I'm using Git LFS with Azure DevOps Services and I get errors when pulling files tracked by Git LFS.
A: Azure DevOps Services currently doesn't support LFS over SSH. Use HTTPS to connect to repos with Git LFS tracked files.
Q: How can I use a non-default key location, i.e. not ~/.ssh/id_rsa and ~/.ssh/id_rsa.pub?
A: To use keys created with ssh-keygen in a different place than the default, perform these two tasks:
- The keys must be in a folder that only you can read or edit. If the folder has wider permissions, SSH will not use the keys.
- You must let SSH know the location of the keys. You make SSH aware of keys through the
ssh-addcommand, providing the full path to the private key.
On Windows, before running ssh-add, you will need to run the following command from included in Git for Windows:
This command runs in both PowerShell and the Command Prompt. If you are using Git Bash, the command you need to use is:
You can find ssh-add as part of the Git for Windows distribution and also run it in any shell environment on Windows.
On macOS and Linux you also must have ssh-agent running before running ssh-add, but the command environment on these platforms usuallytakes care of starting ssh-agent for you.
Q: I have multiple SSH keys. How do I use different SSH keys for different SSH servers or repos?
A: Generally, if you configure multiple keys for an SSH client and connect to an SSH server, the client can try the keys one at a time until the server accepts one.
However, this doesn't work with Azure DevOps for technical reasons related to the SSH protocol and how our Git SSH URLs are structured. Azure DevOps will blindly accept the first key that the client provides during authentication. If that key is invalid for the requested repo, the request will fail with the following error:
For Azure DevOps, you'll need to configure SSH to explicitly use a specific key file. One way to do this to edit your ~/.ssh/config file (for example, /home/jamal/.ssh or C:Usersjamal.ssh) as follows:
Windows Global Ssh Config
Q: How do I fix errors that mention 'no matching key exchange method found'?
A: Git for Windows 2.25.1 shipped with a new version of OpenSSH which removed some key exchange protocols by default.Specifically, diffie-hellman-group14-sha1 has been identified as problematic for some Azure DevOps Server and TFS customers.You can work around the problem by adding the following to your SSH configuration (~/.ssh/config):
Replace <your-azure-devops-host> with the hostname of your Azure DevOps or TFS server, like tfs.mycompany.com.
Q: What notifications may I receive about my SSH keys?
A: Whenever you register a new SSH Key with Azure DevOps Services, you will receive an email notification informing you that a new SSH key has been added to your account.
Q: What do I do if I believe that someone other than me is adding SSH keys on my account?
A: If you receive a notification of an SSH key being registered and you did not manually upload it to the service, your credentials may have been compromised.
The next step would be to investigate whether or not your password has been compromised. Changing your password is always a good first step to defend against this attack vector. If you’re an Azure Active Directory user, talk with your administrator to check if your account was used from an unknown source/location.
Q: What do I do if I'm still prompted for my password and GIT_SSH_COMMAND='ssh -v' git fetch shows no mutual signature algorithm?
Jenkins Ssh Global Configuration
A: Some Linux distributions, such as Fedora Linux, have crypto policies that require stronger SSH signature algorithms than Azure DevOps supports (as of January 2021). There's an open feature request to add this support.
Git Global Ssh Config
You can work around the issue by adding the following code to your SSH configuration (~/.ssh/config):
Replace ssh.dev.azure.com with the correct host name if you use Azure DevOps Server.
